Bitcoin’s Quantum Risk Moves From Theory to Timeline
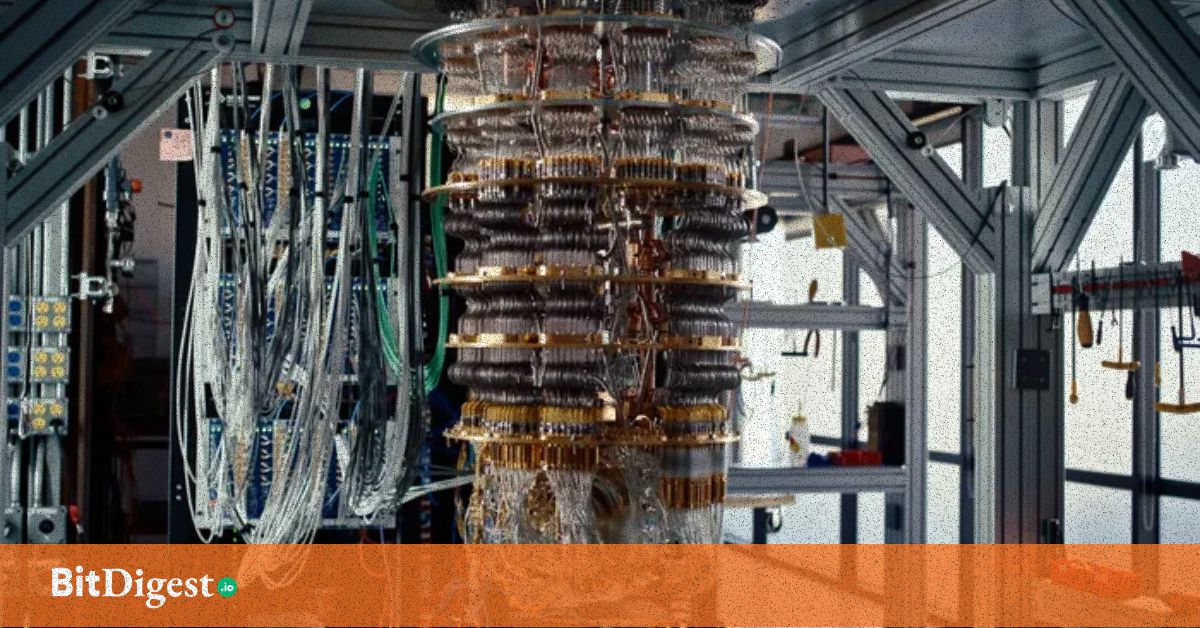
Concerns around quantum computing and Bitcoin security are gaining renewed attention following recent advances in error correction and shifting timelines from major technology firms. While no existing quantum computer can break Bitcoin today, developments suggest the conversation is moving from distant theory toward long-term planning.
At the center of the issue is Bitcoin’s reliance on elliptic curve cryptography, specifically secp256k1. In a sufficiently advanced quantum environment, Shor’s algorithm could theoretically derive private keys from public keys, undermining the foundation of Bitcoin’s transaction security.
A Breakthrough That Changed the Conversation
The renewed urgency stems in part from progress by Google, which demonstrated a key milestone in quantum error correction using its Willow processor. By scaling error-correcting codes, the company showed that logical error rates could decrease as systems grow; an essential requirement for building fault-tolerant quantum machines.
Alongside this, Google announced plans to migrate its own systems to quantum-resistant cryptography by 2029. While this timeline is precautionary, it signals that large institutions are no longer treating quantum threats as purely theoretical.
Where Bitcoin Becomes Vulnerable
Bitcoin is not uniformly exposed, but certain transaction patterns create risk over time. When a Bitcoin transaction is broadcast, it reveals the sender’s public key. In a future scenario where quantum computers are sufficiently powerful, an attacker could intercept this data, derive the private key, and attempt to submit a competing transaction before confirmation.
Estimates of potentially exposed Bitcoin vary widely. Some analyses suggest that up to a third of the supply could face long-term risk due to address reuse or legacy formats, while more conservative estimates place meaningful exposure much lower. In practice, most of these coins are not immediately vulnerable unless they are actively spent.
A Slow but Deliberate Response
The Bitcoin developer community has begun exploring early mitigation steps. One proposal, known as BIP 360, introduces a new transaction structure that reduces long-term public key exposure by relying on Merkle roots rather than traditional key-based spending paths.
This approach is designed to be incremental—compatible with existing systems while preparing for future integration of post-quantum signature schemes. However, any meaningful upgrade to Bitcoin requires broad consensus, making the process inherently slow.
Time Is Still on Bitcoin’s Side
Despite the headlines, most experts agree that a quantum computer capable of breaking Bitcoin’s cryptography does not yet exist. Estimates for such a machine—often referred to as “Q-Day”—generally fall in the 2030s or later, depending on continued breakthroughs in scaling and error correction.
Bitcoin also benefits from certain structural advantages. Its proof-of-work system, based on SHA-256, is less vulnerable to quantum acceleration, and users can already reduce risk by avoiding address reuse and keeping public keys unexposed until necessary.
A Question of Preparation, Not Panic
The growing discussion around quantum risk reflects a broader shift in how the industry approaches security. Rather than reacting to an immediate threat, developers and institutions are beginning to plan for a future where current cryptographic assumptions may no longer hold.
For Bitcoin, the challenge is not just technical but social, balancing the need for upgrades with the network’s decentralized governance model. The outcome will likely unfold over years, not months.
Quantum computing does not yet threaten Bitcoin in practice, but it is no longer an abstract concern. As timelines shorten and research progresses, the focus is shifting toward ensuring the network can adapt before the threat becomes real.
.svg)

.svg) SHARE TO FACEBOOK
SHARE TO FACEBOOK SHARE TO TWITTER/X
SHARE TO TWITTER/X SHARE TO LINKEDIN
SHARE TO LINKEDIN SEND TO MAIL
SEND TO MAIL





.svg)


.svg)